CVE matching¶
ONEKEY automatically matches vulnerabilities with the components found in your firmware.
Vulnerabilities are collected from multiple databases: NIST NVD (National Vulnerability Database) and OSV (Open Source Vulnerabilities). (1)
- NVD uses CPE-based component identifiers. If the platform cannot determine the correct CPE for a component, you can edit the Vendor and Product fields to improve NVD matching results. OSV uses Package URLs (purls) derived from package manager metadata (npm, Maven, etc.) and other sources such as embedded binary provenance information.
If the same vulnerability appears in multiple databases but with a different vulnerability identifier, the platform creates one entry and lists the alternative vulnerability identifiers under Ids.
CVE details¶
To see the vulnerabilities found in a particular firmware, enter Firmware analysis view and click the CVEs tab.
Info
ONEKEY uses Automated Impact Assessment to automatically determine if a vulnerability is relevant or not for specific firmware, so only applicable vulnerabilities are displayed.
For a list of vulnerabilities found in all uploaded firmware, select the Search in tab in the top menu bar and click CVE.
Click on a vulnerability to learn more about it.
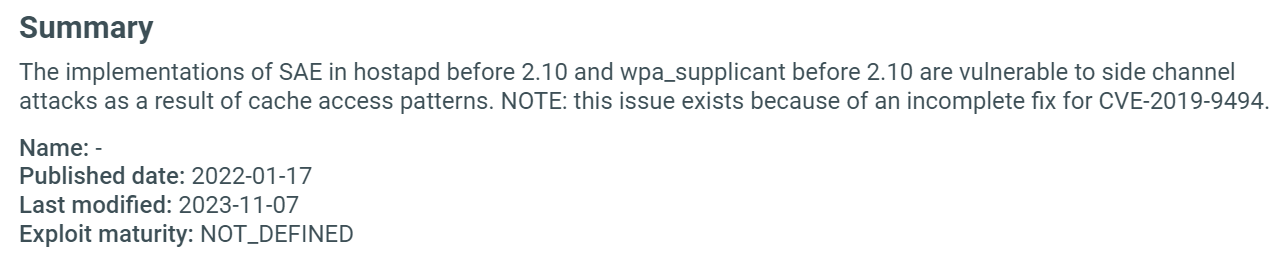
Summary¶
Short description of the vulnerability and basic information, such as the date it was published, the unofficial name given by the discoverer, CWE, and EPSS information. (1)
-
The CWE (Common Weakness Enumeration) identifies the class of weakness being exploited – for example, a buffer overflow, improper authentication, or use-after-free. Click on the CWE ID to read the full weakness description.
EPSS (Exploit Prediction Scoring System) shows the probability of a vulnerability being exploited. The greater the score the higher the chance for an exploit. The percentile means the proportion of all scored vulnerabilities with the same or a lower EPSS score.1 Click on the question mark to learn more.
Fields are shown only when data is available for the given vulnerability.
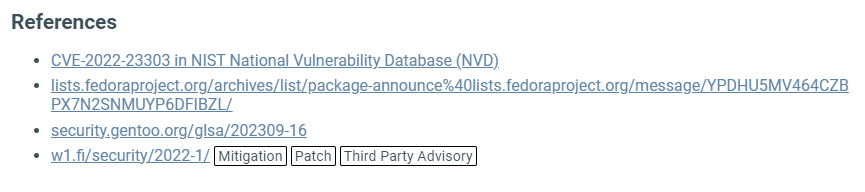
References¶
List of websites from where the platform got the displayed information, along with some further reading about the vulnerability.
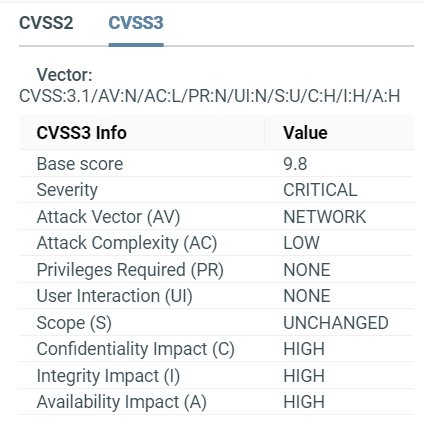
CVSS¶
CVSS stands for Common Vulnerability Scoring System; it shows the risk factor of a vulnerability by assigning it a score from 0-10 (0 means no risk, 10 means critical risk). CVSS also includes other details like attack complexity, integrity impact etc.
ONEKEY displays CVSS2, CVSS3, and CVSS4 (where available) vulnerability information.
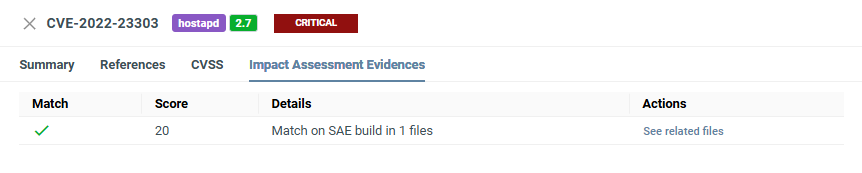
Automated Impact Assessment¶
Here you can see how the Automated Impact Assessment match score was calculated and the evidence behind the score and decision.
Compare CVEs¶
You can compare vulnerabilities across two separate firmware images or across multiple analyses of the same firmware – for example, to track how your vulnerability exposure changes between versions.
See Compare analyses to get started.
CVE Matches vs. CVE Entries
A CVE Entry is a vulnerability record in the CVE database – it describes the vulnerability itself. Even if a CVE affects multiple components in the compared firmware, it counts as one entry.
A CVE Match is one occurrence of a specific CVE in a component. If the same CVE affects multiple components, each affected component counts as a separate CVE match.
For example, if CVE-2024-53141 affects two Linux kernel versions in the compared firmware, this counts as 2 CVE matches but only 1 CVE entry.
Calculating severity¶
Severity is based on the CVSS3 score:
| Severity | Severity Score Range |
|---|---|
| Informational | 0.0 |
| Low | 0.1-3.9 |
| Medium | 4.0-6.9 |
| High | 7.0-8.9 |
| Critical | 9.0-10.0 |