SBOM management¶
Summary
ONEKEY automatically generates an SBOM from the firmware image during analysis. You can enrich it by importing an external SBOM and editing individual components. Export the result in CycloneDX or SPDX format, optionally with VEX vulnerability statements.
As part of the analysis process, ONEKEY generates a Software Bill of Materials (SBOM) from the uploaded firmware image. The SBOM reflects the contents of the Components page on the platform, which is populated using multiple detection methods such as package manager enumeration, binary analysis rules, lock file parsing, and RTOS component detection.
For each detected component, the platform records details such as:
- name
- version
- associated files
- Common Platform Enumeration (CPE) strings
- license information
Import SBOM¶
You can attach an SBOM file to your firmware during the upload process.
This enables ONEKEY to identify components or to compare and assess the quality of the SBOM. Supported SBOM formats are:
- CycloneDX JSON (versions 1.2 - 1.6)
- CycloneDX XML (versions 1.1 - 1.6)
The SBOM file must be uploaded with the firmware image; it is not possible to upload the SBOM at a later point.
ONEKEY validates the SBOM as a preliminary step before the analysis begins – not at upload time. If there are any problems with the SBOM the analysis won't proceed. Errors are reported in the Analysis Overview page.
To upload just an SBOM, drag and drop it to the SBOM upload area. In Firmware analysis view, binary specific results are hidden or grayed out for SBOM-only uploads.
By importing an SBOM you can supplement or validate the platform's own component detection. This is useful when you have a build-system-generated SBOM and want the platform to incorporate it, or when you want to cross-reference the platform's auto-detected components against a known reference.
Good to know
- Attaching an SBOM to a firmware does not disable automatic component detection. Instead, the platform creates the component list using both sources. Any issues with the SBOM (such as invalid or missing data) will cause the analysis to fail.
- When an imported SBOM contains a component already detected by the platform, the results are merged. View the integration details under the Evidences tab.
- If a component is included in the imported SBOM but not detected by the platform, it will be listed as containing 0 files.
- ONEKEY cannot perform Automated Impact Assessment on CVEs that have been matched with components that were imported from an SBOM file but not detected by the platform.
Check component details¶
The Components page lists everything the platform has identified in the firmware—components from auto-detection, from an imported SBOM, and any manually added entries.
Select a component from the table to open the Component details. Here you can see,
- some basic information about the component (Overview tab),
- the files it contains (Files tab),
- the CVEs found (CVEs tab),
- and a list of items that indicate the methods and sources used in identifying the selected component (Evidences tab).
Component editing¶
If a component is not detected, or is detected with incorrect metadata, CVE matching will be incomplete or inaccurate. You can correct this directly on the Components page:
- Select a firmware.
- Navigate to the Components page.
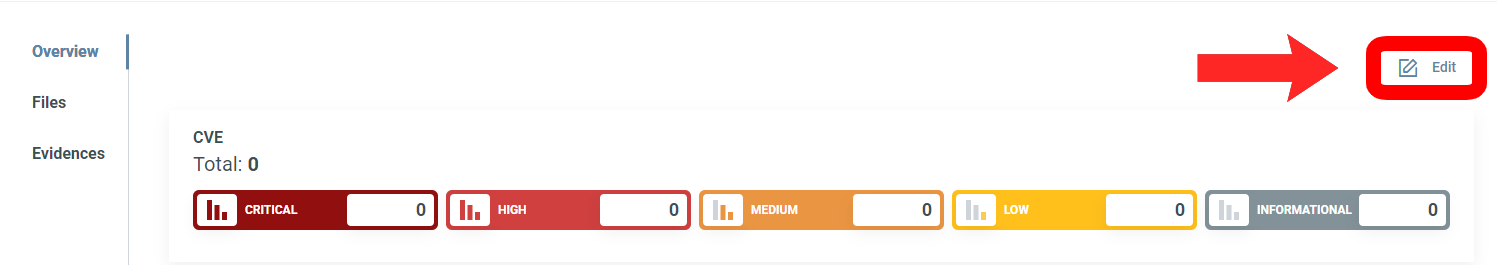
- Click on a component.
- Click Edit.
In most fields, you can enter any text without restrictions, but for Tags you can only choose from the items in the dropdown menu.
To edit the CPE string, update the Vendor and Product fields.
How component identifiers affect vulnerability matching
The platform uses multiple methods to match components against vulnerability databases.
CPE-based matching (NVD): For components matched against NVD, the platform derives a CPE string from the Vendor and Product fields. The accuracy of these fields directly controls the quality of NVD matching.
Purl-based matching (OSV): Package URLs (purls) are derived from package manager metadata (npm, Go, Maven, etc.) and other sources such as embedded binary provenance information. Editing Vendor and Product adds CPE-based NVD matches on top of any existing purl-based OSV matches — it does not replace or remove them. Purls cannot be edited directly.
Components sourced exclusively from an imported SBOM follow the same matching logic, but Automated Impact Assessment cannot run on them because there are no binary files to analyze.
After any change to Vendor or Product, rerun the analysis to apply the updated CPE and see revised NVD matching results.
For the Licenses field you can select an item from the dropdown menu, but you can also enter your own text.
To save your changes click Submit, to discard the changes click Cancel.
The Name, Version, and Update fields cannot be left empty. After editing, adding, or deleting a component, rerun the analysis for the changes to take effect.
Add components¶
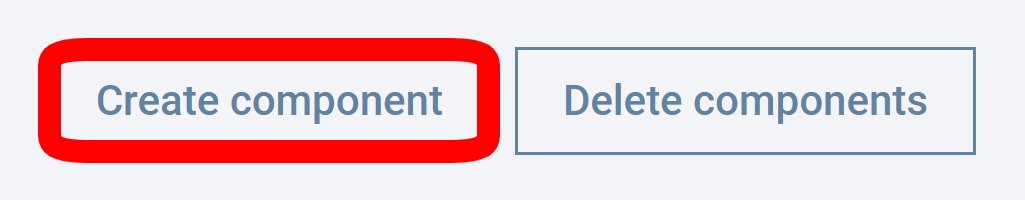
- Click Create component on the Components page.
- Enter component info. The Name, Version, and Update fields cannot be left empty.
- Click Submit.
Delete components¶
- On the Components page, Check the boxes next to the components you want to delete.
- Click Delete components.

Alternatively, if you want to delete only one component, you can click on Edit on the Component details popup, then select Delete.
Export SBOM¶
The exported SBOM is a snapshot of the current Components page, including any manual edits.
To download an SBOM, select a firmware and click the Download SBOM button on any page in Firmware analysis view:
A popup window will open. Here you can select:
- The SBOM format.
- The file format.
- The version of the SBOM file.
- Whether the files should be included.
Once you are ready, click on the Download button. Components with UNKNOWN or AMBIGUOUS versions have an * for version in their CPE string.
Available SBOM formats for download
- CycloneDX JSON (versions 1.2 - 1.7)
- CycloneDX XML (versions 1.1 - 1.7)
- SPDX JSON (version 2.3)
- SPDX XML (version 2.3)
VEX Export¶
Exporting VEX information can, for example, support compliance with certain cybersecurity regulations (such as the Cyber Resilience Act), as it provides documented statements of vulnerability assessments and mitigations.
To export a VEX‑enhanced SBOM, select CycloneDX for the SBOM format and select which details to include using the checkboxes.
Global components page¶
The Global components page provides a cross-firmware view of all components identified across your uploaded firmware images. This is useful for finding all firmware that contain a specific component or version – for example, when assessing the reach of a newly published vulnerability. Click Search in from the top menu bar, then select Components. For more information, see Global Search.
Note
You cannot edit components on the Global components page.
Quick reference¶
| Feature | Details |
|---|---|
| Import | You can attach an SBOM at upload time only – SBOM cannot be added to an existing firmware. SBOMs are validated at analysis start; errors are reported in the Analysis Overview. |
| Import + auto-detection | Both sources are merged into a single component list. Components from the SBOM that the platform did not detect independently are listed with 0 files. |
| SBOM-only upload | Uploading an SBOM without a firmware binary is supported; binary-specific results are hidden or grayed out. |
| Edit components | Update name, version, vendor, product, licenses, and tags. Add/delete components. Requires reanalysis to update CVE matching. |
| Vulnerability matching | NVD matching uses a CPE derived from Vendor and Product. OSV matching uses Package URLs (purls) from package manager metadata and other sources. |
| Automated Impact Assessment | Not available for components sourced exclusively from an imported SBOM (no binary evidence). |
| Export | Download from any page in Firmware analysis view. |
| VEX export | CycloneDX only. Pairs the SBOM with vulnerability assessment. |
| Global components page | Cross-firmware view of all components. Component editing is not available. |